We took a close look at iodéOS, which is based on LineageOS. Can the privacy friendly operating system fulfill its promises? Read our test!
As already mentioned, iodéOS is an Android operating system based on LineageOS with a special focus on privacy. The manufacturer claims that the user can use the full comfort of Android without being spied on by Google and other data octopuses all the way. At least that is what the founder of iodé, Antoine Maurino, promises us.
 The increasingly frequent data scandals at Google or Facebook, to name just the two most important ones, usually seem „far away„. But more and more people seem to be slowly realizing that they, too, are a small but important part of this constantly expanding data collection.
The increasingly frequent data scandals at Google or Facebook, to name just the two most important ones, usually seem „far away„. But more and more people seem to be slowly realizing that they, too, are a small but important part of this constantly expanding data collection.Most of the time, it starts out small. An app here, another one there. And then, before you know it, you have countless apps installed on your Android phone.
But all these apps have one thing in common. That’s right, they collect data. Your data! And mostly behind your back. Did you know that Google alone requests location information and other data from your Android smartphone 340 times in a 24-hour period?
iodéOS: You can also install the privacy-friendly operating system yourself
The good news comes right at the beginning. You do not necessarily have to buy a smartphone from Antoine Maurino to use the iodéOS. However, if you want to save yourself the trouble of having to install the privacy-friendly operating system yourself, there is an appealing selection of used and new Android smartphones on the iodé site. Currently, the iodéOS is available for download for the following phone models:
- Fairphone (FP3, FP3+)
- Teracube (2E)
- Xiaomi (Mi 9)
- Samsung (S9, S9+, Note9)
- Samsung A5 2017
- Sony Xperia (XA2, XZ1, XZ2, XZ3)
 Antoine Maurino provided me with one of his used Samsung A5 (2017) with preinstalled iodéOS to thoroughly evaluate it for this article.
Antoine Maurino provided me with one of his used Samsung A5 (2017) with preinstalled iodéOS to thoroughly evaluate it for this article.But what is the difference to LineageOS after all?
The iodéOS is based on the well-known LineageOS. But what exactly makes the difference? How does the iodéOS presented here differ from LineageOS or even from a „normal“ Android system? Well, for example, there are some important adjustments to avoid data leaks:
- Default DNS server: Google’s DNS replaced by Quad9’s „unblocked“ server.
- A-GPS: supl.google.com replaced by supl.vodafone.com.
- Captive portal login: connectivitycheck.gstatic.com replaced by captiveportal.kuketz.de for connectivity check.
- Dialer: Google default option replaced by OpenStreetMap for phone number lookup.
Small, but yet powerful. These important adjustments help us prevent our smartphone from connecting to Google over and over again. But that alone is not enough, of course. Let’s now take a look at which apps are already preinstalled.
Preinstalled apps in the iodéOS
- MicroG core applications: GmsCore, GsfProxy, FakeStore, Maps API.
- NLP backends for microG: DejaVuNLPBackend (default), MozillaNLPBackend, AppleNLPBackend, RadioCellsNLPBackend, NominatimNLPBackend
- App stores: F-Droid (with F-Droid Privileged Extension) and Aurora Store
- Browser: iodé browser (based on Firefox (Fenix), with Qwant as default search engine and telemetry disabled) instead of Lineage’s default Jelly browser
- SMS: QKSMS instead of the default SMS app from Lineage
- Maps/Navigation: Magic Earth GPS & Navigation (the only pre-installed app which is not open source)
- Keyboard: OpenBoard instead of the AOSP keyboard
- PDF: Pdf Viewer Plus
- Personal notes: Carnet
- Ad/malware/data leak blocker: iodé. (currently not open source)
- iodé News: to inform users about new developments, and a FAQ.
iodé’s native blocker against ads, malware and data leakage
 If you have ever tried microG or a Google free Android, you know that it sometimes takes quite a while to install everything correctly and then set it up. Antoine Maurino and his team from iodé take this work off the user’s hands.
If you have ever tried microG or a Google free Android, you know that it sometimes takes quite a while to install everything correctly and then set it up. Antoine Maurino and his team from iodé take this work off the user’s hands.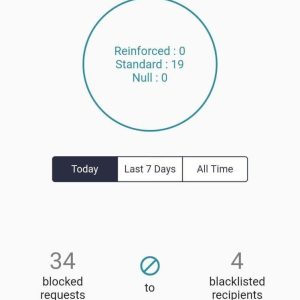
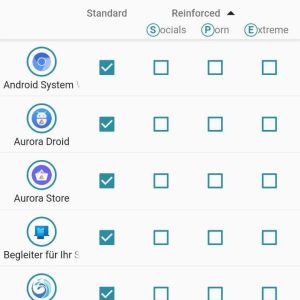
The iodé app is a particularly deeply integrated interface that scans the Internet communication of all apps installed on the device in real time. Access to advertising, malware, spam, spyware and trackers is blocked by default and very reliably by means of a so-called „hosts blocklist„.
A hacking principle called „man-in-the-middle attack“ and the iodé app
So, by default, the ad blocker integrated in iodéOS runs permanently on our device. It is based on a hacking principle called „man-in-the-middle attack“ (MITM), with the goal of intercepting the communication between two endpoints. This also includes the huge advantage that you can still use either a „VPN“ or even an additional ad blocker on your smartphone.
„iodéOS relies on an open-source collaborative database to keep its blacklist up-to-date. Following this collaborative blacklist, iodé maintains its own blacklist (see FAQ). You will soon be able to add your own recipients to the blacklist through the iodé app interface.“ (iodé)
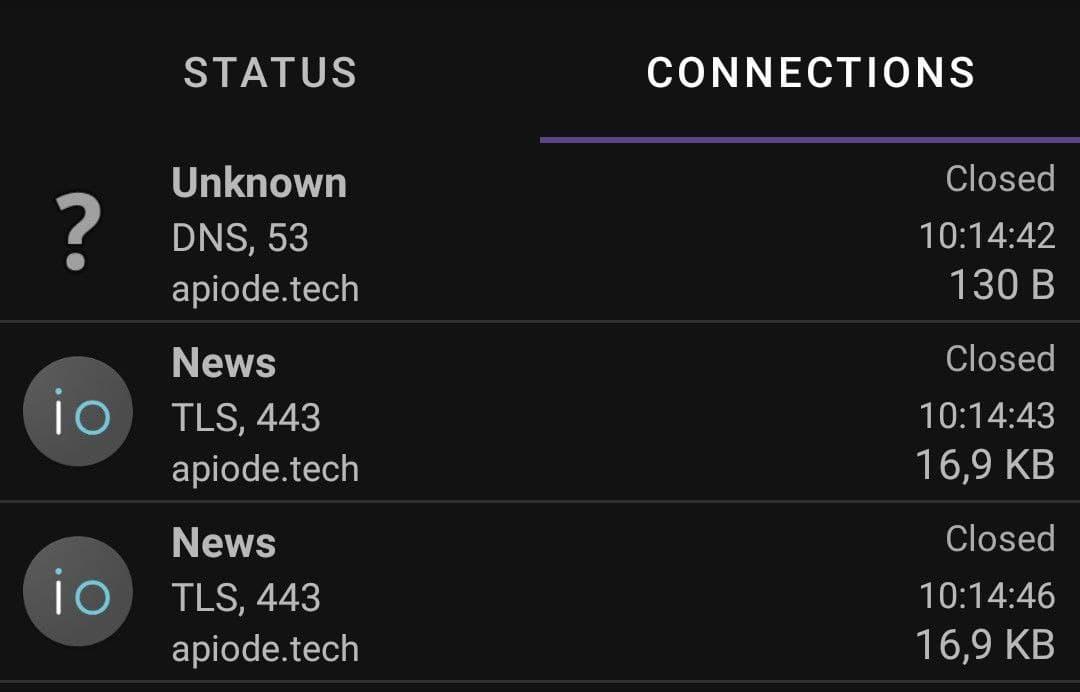 The interception is guaranteed to happen only locally on our device. I was able to confirm this quite quickly with PCAPdroid (logging and examining the connections made by user and system apps) and ADB-Logcat. All data traffic of installed apps is meticulously recorded by the app and protected with the support of a very extensive host blocklist. This host blocklist is provided by „Energized Protection„, among others.
The interception is guaranteed to happen only locally on our device. I was able to confirm this quite quickly with PCAPdroid (logging and examining the connections made by user and system apps) and ADB-Logcat. All data traffic of installed apps is meticulously recorded by the app and protected with the support of a very extensive host blocklist. This host blocklist is provided by „Energized Protection„, among others.iodéOS: data protection does not always have to be complicated
I think the iodé team around Antoine Maurino has really done a very good job here. It is very easy to find your way around the iodé app itself. Every app installed on our device is clearly displayed. One click is enough to open the app and you can see exactly which app has connected how often, when and with whom (very important) in real time. And of course, for each app you can individually set how strict the protection should be. You can also whitelist individual apps if you want. The ability to add host filter lists yourself is planned and will be implemented soon.
 This Android operating system is primarily aimed at users who care about protecting their privacy. As already mentioned, this is guaranteed by iodé’s integrated adware, malware and data leakage blocker. The fact that microG and the Aurora Store are also firmly integrated into the system as an important component makes the OS interesting for Google deniers. It does not matter for what reasons one wants to do without Google. And since not all of us know how to install a custom ROM or even how to root it, a smartphone with preinstalled iodéOS is really a very nice thing.
This Android operating system is primarily aimed at users who care about protecting their privacy. As already mentioned, this is guaranteed by iodé’s integrated adware, malware and data leakage blocker. The fact that microG and the Aurora Store are also firmly integrated into the system as an important component makes the OS interesting for Google deniers. It does not matter for what reasons one wants to do without Google. And since not all of us know how to install a custom ROM or even how to root it, a smartphone with preinstalled iodéOS is really a very nice thing.But as mentioned at the beginning: If you own one of the compatible phones (see list above), you can also install this operating system on your own (basic knowledge required).
Always up to date with the iodé news app
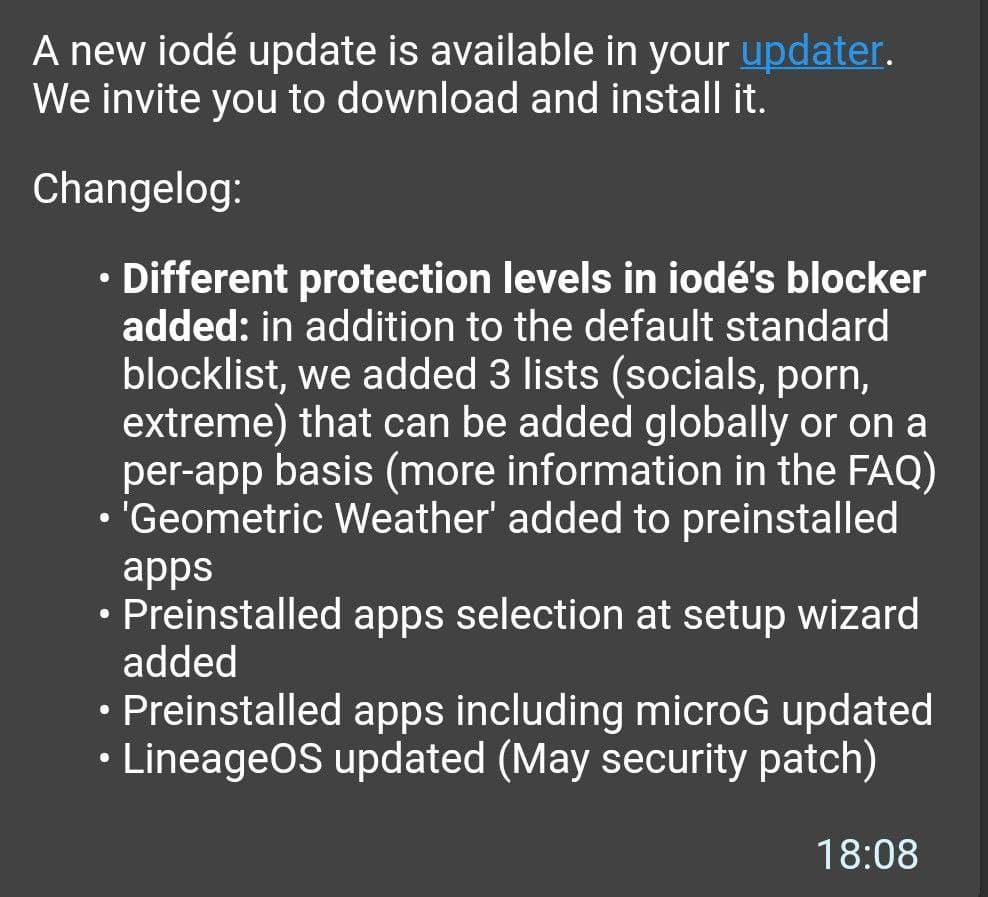 With an Android operating system, it is important to always keep it up-to-date. Regular updates are a must. iodé clearly scores in this aspect as well. On the one hand, the manufacturer regularly delivers security patches (LineageOS). In addition, the operating system itself is up to date with Android 10. The iodé news app, which is also integrated into the system, informs us about all that and much more. Oh yes, I almost forgot. :D Of course, an update to Android 11 is already in progress.
With an Android operating system, it is important to always keep it up-to-date. Regular updates are a must. iodé clearly scores in this aspect as well. On the one hand, the manufacturer regularly delivers security patches (LineageOS). In addition, the operating system itself is up to date with Android 10. The iodé news app, which is also integrated into the system, informs us about all that and much more. Oh yes, I almost forgot. :D Of course, an update to Android 11 is already in progress.A final rating – surprisingly good with room for improvement
If you want to pay more attention to data protection on your smartphone in the future, then you are definitely looking at the right thing. If you don’t know how to open a bootloader, flash a new operating system (custom ROM), or how to root your device and configure microG correctly, you certainly won’t go wrong here. In that case, I think you should take a closer look at the phone models provided by iodé. If you are not an expert and have a suitable device, you can also install iodé yourself.
The iodé smartphones and the iodéOS: there are a few negative aspects
There are also a few negative points. However, they do not really matter in my opinion. First, there is the fact that not all installed apps are open source. Antoine Maurino assured me that at least the integrated ad/malware and data leak blocker from iodé will normally be open source by next year. So the motto is wait and see.
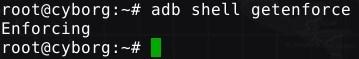
However, the bootloader on my Samsung A5 (2017) was closed again and the device is not rooted yet. Why should it be? Everything fits as I got my hands on the smartphone. Just unpack it, turn it on and start using it right away. Because of the missing Google services and microG that is already preconfigured for us, even the initial setup is a breeze. By the way, it would be worth mentioning that SELinux is not „permissive“ in this Android operating system (as first assumed), but has been set to „enforced“.
A few last words about Antoine Maurino and iodé
 Finally, there are one or two things I would like to point out. Neither tarnkappe.info nor I have received any money from Antoine Maurino or iodé for this article. Likewise, no „affiliate links“ of any kind were set by us.
Finally, there are one or two things I would like to point out. Neither tarnkappe.info nor I have received any money from Antoine Maurino or iodé for this article. Likewise, no „affiliate links“ of any kind were set by us.Tarnkappe.info