We spoke with Peer Heinlein of the crypto email service mailbox.org. But there is much more at stake. They're expanding their business model.
We recently spoke with Peer Heinlein, founder of the crypto e-mail service mailbox.org. But it’s about much more than mail: the company is expanding its business model.
A detailed conversation with the CEO of mailbox.org
We enjoyed an extended conversation with Peer Heinlein, the founder and managing director of the e-mail provider mailbox.org. But not only that: Heinlein also runs JPBerlin, a provider for socially and politically engaged people, in addition to Heinlein Hosting, another consulting firm and his own Linux academy. You can read the german version here.
There is a lot of competition among crypto-mail providers, with Posteo’s offices literally just around the corner. Another, Tutanota is based in Hanover, to name just the two best-known German competitors, and there are many more abroad.
But there is more: Heinlein, the law graduate, who used to work as a journalist over the years has grown into the role of an entrepreneur, and he also lobbies on his own behalf. His topics include the increasing hunger of the German authorities for access to online services that manage their customers‘ data. A recent example is the ongoing revision of the German Telecommunications Act (TKG). If the EU gets its way, all providers would have to integrate official backdoors for the authorities. IT security or digital seclusion would no longer be possible.
Heinlein and mailbox.org & Co want to stay in Europe.
Within the EU and, of course, in his home city of Berlin. We want to know why.
Tarnkappe.info: Hello Peer, would you like to introduce yourself?
Hello Lars! Thank you for the interview and for the fact that you and your readers are so interested in our work. I’m currently 44 years old and live with my family in Berlin. I learned being a lawyer and journalist, but I have been a full-time IT administrator, managing director and Linux expert for more than 25 years. I feel very privileged that my current job allows me to do all the things I am passionate about.
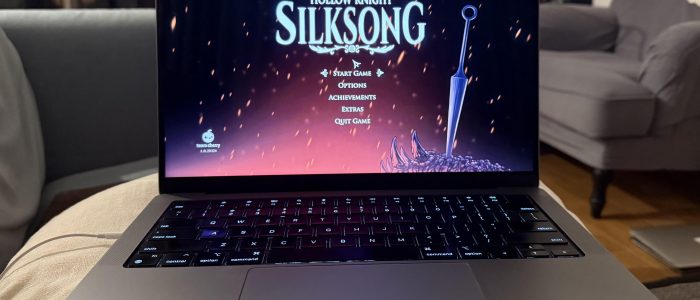
mailbox.org was created in 2013 as a reaction to the Snowden affair

Tarnkappe.info: JPBerlin started back in 1989. What did they deal with in the beginning, and what are they doing today? What has been your motivation for founding the company? And why mailbox.org?
“JPBerlin” used to be the computer mailbox of Junge Presse Berlin e.V., an association of school newspapers in the city of Berlin. I was doing a lot of work with school newspapers, later I also worked as a professional journalist. In 1990 I joined the Junge Presse Berlin and took over their mailbox. That’s where my strong interest in freedom of thought and expression comes from: censorship by schools was a real issue back then.
To this day, this computer mailbox exists as “jpberlin.de”, making it one of the oldest providers we have in Germany. Even though we had to separate everything from Junge Presse Berlin in the mid-1990s in order not to endanger the non-profit status, I still consider it a non-profit project in the sense of the original association.
In the context of the Snowden affair in 2013, our desire grew to build an international, scalable mail provider that would set new standards in terms of security, transparency and freedom from advertising. So we founded mailbox.org.
In addition to our day-to-day work as a provider, Heinlein Support is actually a Linux consulting company: We run our own academy and help professional admins with all kinds of questions about Linux servers in the data center.
“The worst case scenario would happen if sensitive data about the backdoors became public. The threat of a self-inflicted IT security breach caused by the state is huge.“

Tarnkappe.info: In the name of fighting international terrorism, the EU plans to attack the encryption of messengers and e-mail providers. Is it actually possible to have secure communication and future backdoors for authorities at the same time?
Every backdoor weakens the security of a device and no one can seriously guarantee that backdoors will not be abused and exploited. If sensitive data on how these backdoors are implemented became public, the threat of a self-inflicted IT security breach caused by the state is huge.
At the same time, we must ensure government agencies do not abuse their authority. I have no problem with the police and the public prosecutors doing their investigative work, I do want them to be able to do their jobs. But their actions must be legal and thus controllable, transparent and under judicial supervision.
In the end, however, implementing backdoors will also be a big technical challenge: There will always be providers abroad who would not be subjected to such measures, no matter what German providers are forced to. That is also why criminal investigators focus more on access providers who sell internet connections and collect all connection data, rather than on service providers like mailbox.org.
The German state wants more and more control over the internet
Tarnkappe.info: Why do people want to make private communication increasingly difficult, what’s the background? Is it really about fighting crime and terrorism?
That’s a difficult question because I do not want to engage in speculation and conjecture. In the last 20 years, many countries have reacted to the development and growth of the internet. And states and law enforcement agencies have a legitimate interest in knowing what is going on there. I don’t think that’s wrong either – I also want a state to protect democracy, its institutions and us as citizens.
But some states have gone too far and regularly control and censor internet communication. We are still a long way from that in Germany, but we can also feel the general trend towards increasingly targeted access, towards more and more control. We have to be vigilant, because if we don’t push back, it will result in an attack on free communication and the fundamental rights of citizens.
It is normal that those in charge want to use the technical means available. But it requires restraint not to abuse them, to “only” act within the framework of applicable law. As history has shown, not every investigator follows those rules.
No one leaves Germany “just like that“
Tarnkappe.info: What impact will this have on German e-mail providers? Will you migrate if this is introduced EU-wide? What other options do you have?

No, we will not leave. We have strong roots in Germany and we do not intend to go abroad. And it is important to lead the debate here, to build up pressure and to intervene in a formative way so that real alternatives can be created. I want to shape society, not flee from it.
We are actively working against certain developments and have actively participated in the debate on the forthcoming Telecommunications Act (TKG). But I am not seeing any ultimate totalitarian measures being implemented on the EU level yet, so there is no reason to go abroad.
Anyway, you don’t “just move mailbox.org somewhere else”: you need a big team to run it. We currently have fifty employees who are on their toes day and night. And only because this team is so well-coordinated, works independently and is technically up to date we can take the time to develop new things or spend weeks doing unrewarded but important political lobbying on the TKG.
Why should offshore headquarters or anywhere in Russia be safer for us?
Tarnkappe.info: Why did you decide on Germany as a location in the first place? Many providers that are considered safe are officially based offshore or in Russia, etc.
Well, I was born and raised in Berlin, and our company is based on the former mailbox systems of the Junge Presse Berlin. So everything here is “dit is Balin, wa?” (“Thats how we do it here in Berlin”) and it will and should stay that way.

But why should “offshore” or “in Russia” be in any way safer? These days, the Russian state is censoring the internet centrally and has blocked access to mailbox.org. I do not understand how anybody could call that a better or safer location. And what about the state of law in Russia? In our previous disputes with Russian authorities and the secret service FSB we did not get the impression that the Russian legal process can be relied on much.
To be quite honest: even if we see many efforts in Germany right now that target our fundamental, constituional rights and that we need to defend ourselves against, we still live in an incredibly well-organised, law-abiding and constitutional state, and we do enjoy a very high level of protection here. We are definitely very far away from law-bending authorities, censorship or a dictatorial police state.
More than just e-mails: mailbox.org sees itself as a communications provider
Tarnkappe.info: mailbox.org is shifting from an e-mail-only to a multifunctional provider. You have a video conferencing system on offer, XMPP servers, cloud storage, calendars, etc. Is this a unique selling point, or why did you expand your services?
From the very beginning, we did not see ourselves as an “e-mail-only provider”, but more as a communications provider, as the European, data-protecting alternative to Gmail & Co. Of course, this is a bit like David against Goliath but we know that Google will never have to tremble with fear because of us. But we show that there are very good alternatives and we do not do lazy compromises.
Our company has been in the e-mail business for 30 years, but has always operated other services as well. So why not offer people all that they may need for their communication?
Jitsi Meet only offers confidentiality under certain conditions
Tarnkappe.info: Do people really need your video conferencing system if it can be done for free with Jitsi Meet?

Even our current Jitsi solution offers more confidentiality because it is encrypted and only runs through our own servers. All rooms require explicit login and registration, which prevents mistakes and phishing attacks. Since we also provide video conferencing for schools and their classes, reasonable security, data protection, access protection, reliability and support are necessary.
But Jitsi is only a temporary solution for us: because we operate the video conferencing platform for the federal state of Berlin, we are able to gain a lot of experience and know-how. And since summer 2020, we have been developing our own video solution, extremely secure and scalable for providers.
It will contain quite a number of unseen features that conference systems users have always been looking for. Federal states and providers have already shown great interest, which shows us that we are definitely on the right track. Our team of programmers is also growing, we have just hired two more Rust developers.
No resources available for implementing mailtrace
Tarnkappe.info: What about Mailtrace? Will this function – automatic evaluation of log files for sending mail – still come? If so, when approximately? And if not, why not?
Mailtrace was a big pet project of mine, but it won’t materialize anymore. We didn’t work on it in four years and have so many other plans and tasks at the moment that we can’t justify throwing developer resources at it. In principle, Mailtrace already existed, it was and still is in use with us and some providers. But too much would have to be done for an end-user interface at mailbox.org.
E-mail addresses of paid accounts are deleted after one to three years.
Tarnkappe.info: 90 days after deleting an account, mailbox.org reactivates the mailbox address for new registrations. Why such a short deadline? Doesn’t that open the door for cybercriminals to misuse the reactivated e-mail address? For example, they could try to order goods under the old address, re-assign passwords, etc.
The grace period after which we reactivate used addresses depends on how long they have been used and at what rate. Addresses from unpaid test accounts are removed from the blacklist after 90 days, for example, because some users forget their test accounts and can no longer re-register their own address. Mail addresses from paid accounts are only deleted after one to three years.
The mailbox.org name space is limited and we have to prevent malicious bots from systematically going through common names, registering them and thus blocking them permanently. By the way: If anyone wants to block an address permanently, they can do so for just 12 EUR per year by keeping the account running in the least-expensive price plan, so like a protection or blocking fee.
No advertising or tracking, but green energy and a political agenda.
Tarnkappe.info: What makes mailbox.org different or possibly even better than the competition of German mail providers? Where do you see your unique selling point?

The business model of mailbox.org focuses on the customers as our users, and not on third-party companies who pay for users’ data collections and exploiting them.mailbox.org, that means noadvertising, no tracking, no transparent customer. We combine all this with using renewable electricity and a clear politico-social mission. And in the end, it’s all based on 30 years of experience and continuity in a solid owner-managed family business, in an industry where many other companies have been founded, sold, bought up and dissolved again over the years.
On the other hand, we look ahead and continue to develop e-mail as a technology: we are particularly proud of a variety of new security functions developed by us. Many of them were so innovative and successful that they were copied by competitors. For example, we were ahead of Google when it came to displaying the SSL dispatch. The fully encrypted INBOX was our idea and has since been copied a few times. With ID4me, we were the first provider to implement this for our users. e-mail is far from dead, it is usable and secure, and you can still do a lot with it today.
mailbox.org operates two data center in Berlin
Tarnkappe.info: Your productive servers are located in a data center in Berlin. About two dozen administrators take care of these systems. Do you only work with dedicated bare-metal servers or also with VPS or KVM devices? Are these systems owned by you or are they rented?
We have two data center in Berlin and take great care to maintain our services redundantly across both of them. The fire at OVH in Strasbourg last week, where one and a half data center were completely destroyed, clearly shows why we need to go to these lengths.
What counts for us is that everything remains under our own control. Electricity and cooling are the only resources that we get from the data center directly. We own and operate everything else ourselves: Servers, network, uplink/peering traffic.
We use virtualised systems almost exclusively – anything else doesn’t make sense anymore. But we also make sure that we are not dependent on just one technology stack.
No third-party access to the data center
Tarnkappe.info: Who has physical access to the servers in the data center? Just your technicians or also data center employees?

The data centers are large halls and rooms with very strict access restrictions and meticulous monitoring. Our cabinets are our property, and no one else is allowed to access them. There are Exceptions only in case of emergencies, for example when it comes to matters of power supply. Even then local administrators have no technical access to our IT systems.
Tarnkappe.info: Do you also have access or influence on the routing as a neuralgic node (router stack) in the data center?
Yes, we operate our own provider-independent IP addresses, a so-called autonomous system (AS). This means we are responsible for the operation and routing of our traffic . Our size and complexity makes it reasonable to do this on our own.
Each of our data center has a fixed uplink via the local data center provider and its own BGP peering with carriers at the Berlin exchange node BECIX, via which we handle a large part of our traffic directly with providers such as Vodafone, Telefonica/O2 or Microsoft.
We route and peer ourselves – and we can take targeted countermeasures if something happens.
“PGP encryption only works if both sides stay up-to-date“.
Tarnkappe.info: When will the industry finally come up with decent e-mail encryption , a solution that doesn’t require a PhD to use it? Enigmail in combination with the GPG suite and Thunderbird is possible but extremely complicated. Let’s not even mention isolated solutions like Protonmail, where both users have to use exactly the same provider.
mailbox.org Guard is easy to use PGP support in the browser,set up fully automatically with one click. Nowadays, every provider could offer sufficiently securely verified and authorised public keys automatically, based on various established key exchange procedures. In this respect, it would already be possible to use automated PGP keys transparently across providers without requiring deeper knowledge of the technology.
So other providers must finally follow suit and offer similar to their users. PGP encryption only works if both sides stay up-to-date. The technical side is no longer an issue, now the customers have to want and ask for it.
The Power of the Federal Network Agency is increasing
Tarnkappe.info: When managing directors are threatened with being taken into custody for “lack of cooperation“, what kind of development are we actually facing? Let’s gaze into a crystal ball: What do you think the legal basis or the entire Web will look like in five or ten years?

Right now, the new TKG, the IT Security Act and all their siblings are being launched. And they show a glimpse of what is to come. It’s hard for security and data protection experts to find positive concepts in that.
Last week, I was invited as an expert to the hearing of the new Telecommunications Act in the Economic Committee of the German Bundestag. Unfortunately I was the only provider there. At the moment, there is a deliberate attempt to lower the bar for regulation and preventive intervention by the Federal Network Agency.
Unfortunately, from the perspective of a provider focuing on data-protection, I cannot see a single positive aspect in the current draft of the new TKG. Currently, more and more hurdles are being imposed on smaller, innovative providers, jeopardising the diversification that we need for a robust, secure and decentralised communication infrastructure. In my eyes, the federal government is sabotaging its own IT strategy that is supposed to promote “digital sovereignty“.
Trying to prevent the worst…
In any case, we will continue with influencing in a constructive manner, while giving our best to prevent the worst outcomes. That has proven to be a long and arduous process, because a lot of the work is done behind the scenes. But that kind of PR is usually not very attractive for the press In our attention-seeking economy only scandals count, not the good deed of preventing one.
The task now is to stop the new TKG and not let our Home Secretary Horst Seehofer go overshoot. The end results will certainly be a measure of things to come in the next few years. And it is currently impossible to say how things will develop over the short term.
Tarnkappe.info: Peer, thank you very much for the detailed interview. And also a big thank you to our readers who submitted many good suggestions and questions for our community interview in advance.
P.S. Here’s the link to the original german version of the interview.
Tarnkappe.info