We had a chat with the operator of the stresser site Free-Boot.to, who calls himself John. It's all about money, envy or competition!??
We recently had a chat with the operator of the booter / stresser website free-boot.to, who calls himself John. The customers are using his service with completely different motivations. Some of them obviously invest their money in order to fight their boredom, others simply think that it’s funny to destruct a website for a while. Some people try to blackmail webmasters, others want to eliminate their competitors. Free-boot.to has with no doubt a lot customers. Apparently each of them has his own story and his own purpose. We tried to learn a bit more about this special sort of projects.
Die deutschsprachige Version des Gesprächs ist hier verfügbar.
John is maintaining free-boot.to, which is nowadays one of the older and well established DDoS-for-hire services in the net. All we know is that he’s male and living somewhere in the USA or Canada. We didn’t ask him for further details, because of course it’s not legal to administrate such a website. And naturally it’s forbidden to use it as well. In Germany you can be punished up to three years of jail in case you violate against the computer sabotage law called § 303b StGB. Using a booter / webstresser is illegal no matter if you pay for its service, or if you use some parts of it for free.
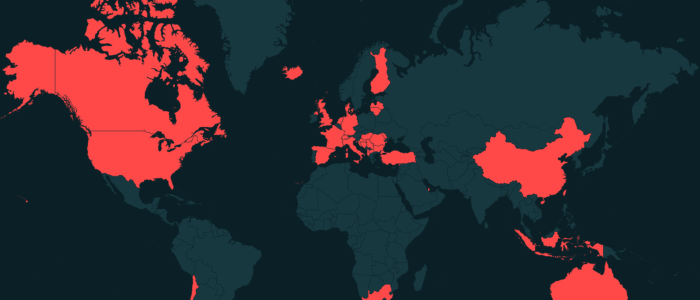
Authorities such as EUROPOL, Interpol, FBI etc. began with their investigations when it was clear, that such illegal services can also cause serious troubles to commercial websites for example from insurance companies, banks or for example e-commerce sites. Now in many countries authorities intensify their investigations. Most likely because the operators of such webstressers earn a lot of money with this sort of dark business. Of course this interview is for educational purposes only, what else did you have in mind? :-)
Organizer has always been interested in such things…
Tarnkappe.info: Hello John and thanks a lot for being part in our interview. For the start: How did you get in touch with this very special topic?
Since a young age, I have been interested in such things, I don’t remember the exact moment. It was a long time ago.
Tarnkappe.info: Okay, and what was your motivation to start free-boot.to?
Back then in December 2017 when we were starting with Freeboot, we wanted to make it completely free and secure with great power.
free-boot.to was made just for fun back in the days, it was free with everything.
Tarnkappe.info: How many people are involved, what are they doing?
I’m not going to discover the exact number, but we have people from support agents to PHP developers and server managers.
Free-Boot.to „can generate a lot money each month“
Tarnkappe.info: Do you have a regular job or is this your main income?
Freeboot can generate a lot money each month, however, I would like to avoid this question.

Tarnkappe.info: I heard rumors, that even some new DDoS-for-hire services start with a sales volume of 10K to 20.000 US-Dollars each month. But let’s talk about something else. Do you have an idea, why the heck so many people are interested into causing troubles to friends and foreigners by taking their websites down for quite a while?
There are many groups of people, some are just doing that for fun, some to win at games, some are getting paid for it, and some only want to test their connection/security there are a lot of purposes.
Tarnkappe.info: Do you think it often happens that companies or people are blackmailed? And in case they don’t pay, do their sites get stressed?
Yes, it does happen. I don’t know how often, but if people do that they most likely want to target bigger sites, they need a lot of power and a lot budget to run such attack.
free-boot.to: We never really paid for an attack script
Tarnkappe.info: Did you code your attack scripts on your own? Or did you buy them instead?
Well, we never really paid for an attack script.
Tarnkappe.info: Or did you grab them in a board (forum)? Maybe you took the source code from someone else in order to improve it?
They are from board, yeah, except Layer7. Those methods are public but edited.
Tarnkappe.info: What’s the main difference between your service and other webstressers?
I don’t check the stresser market anymore, I don’t think there is some huge difference.
free-boot.to: „The competition is not that heavy in my opinion„
Tarnkappe.info: What about the competition, is it heavy? Is it all a matter of the price at the end? Or what’s the decisive point because people choose the one or other provider?
It is not that heavy in my opinion, every stresser has something different. Clients usually choose stresser which they like, fits their needs and is affordable or and reliable for them.
Tarnkappe.info: Did you assemble your service for a special audience for example with special needs? Do you offer a unique feature? Or is it compared with the others notably easy to use it? What I mean: What were the points that have been really important for you while assembling your website?
Well, not really unique features, I don’t really know about something special.

Tarnkappe.info: How do you advertise for your service? Are there any places in the net where you can do that?
We’ve never really advertised like this, although we had paid AD on CyberHub ) several times. Some of our customers record videos on YouTube.
Tarnkappe.info: Have you ever heard about an attack called NDK-flood? If yes, will you include it this year?
I don’t know what NDK-Flood is and it’s the first time I’m hearing this.
 DDoS via server or botnet
DDoS via server or botnet
Tarnkappe.info: Okay, maybe someone tried to confuse us both with this question. What’s your reason not using botnets as well for your service? Do you use rented servers paid with a foreign name? Or are they mostly hacked?
You need to invest a lot of time to build a good botnet. Using Layer4 botnet for stresser is not really worth it. And as for now, I don’t own any botnet and don’t plan to. We are using „rented“ servers.
Tarnkappe.info: Of course not with your real name. Btw.: Which attack mode do you prefer for regular websites? Which band width can you provide at maximum?
Highly depends on type of the website. Regular website is still a long term. I would personally attack it with L7 or flood the backend with L4.
„Nowadays it’s easy to bypass the protection of Cloudflare.“
Tarnkappe.info: How easy or hard is it to bypass the Cloudflare (CF) protection against DDoS attacks? If it’s easy, why is CF still so often used?
Yes, nowadays it’s easy, especially with botnets.
Some people use Cloudflare just to hide Backend IP, some people use rate-limiting and some people like using it as content delivery network (CDN). I don’t really know the exact reasons.
„Fear is, and always be. Rather be paranoid than careless.“
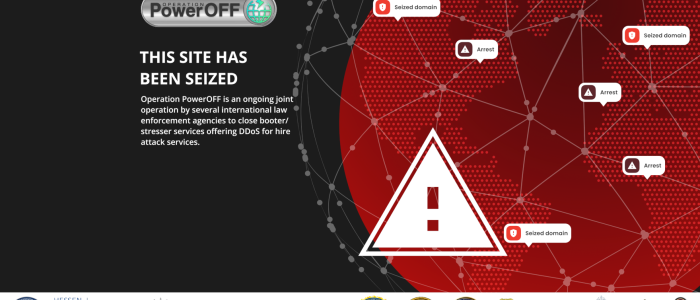
Tarnkappe.info: Before Christmas last year 15 different booter / stresser websites have been taken down by the U.S. Justice Department and the FBI. All domains have been seized, the operators have been arrested. How dangerous is your business nowadays? Your website isn’t the newest as well, so they could observe you as well. Do you have fears?
Not all of the operators have been arrested, this business is dangerous and is not.
Fear is, and always be. Rather be paranoid than careless. :)
Tarnkappe.info: It sounds as if you’ve taken reasonable precautions for free-boot.to. At the moment the police in 15 countries is trying to bust the former users of Webstresser.org. How safe are your customers?
Customers are safe and are not. We allow every customer access our site using TOR, pay using Bitcoin and use pseudo email Paying with bitcoin can be done manually using our tickets or using 3rd party site. I highly recommend using TOR Browser for everyone.
DDoS is there going to be even in 5 or 10 years
Tarnkappe.info: Last question. How’s the internet looking like in 5 or 10 years? Will it be an internet with or without webstressers? And what will you do then?
I would say DDoS is there going to be even in 5 or 10 years. I will continue living the same as I’m living now.
Tarnkappe.info: John, thanks a lot for your replies! And kudos to our readers as they’ve send us some good questions for this conversation. The german version of the interview has also been published.
The picture at the start of this interview with free-boot.to was part of an infographic from EUROPOL, thx!
Tarnkappe.info